Introduction
In modern enterprise environments, Kubernetes platforms are often deployed in air-gapped infrastructures to meet strict security, compliance, and data sovereignty requirements. While this setup significantly reduces external attack surfaces, it also introduces operational challenges—especially when it comes to managing container images and application dependencies.
This is where Harbor, an enterprise-grade container registry, becomes a critical component. When deployed on a vSphere Kubernetes Service (VKS) cluster, Harbor provides a secure, internal repository for storing, scanning, and distributing container images without relying on external networks.
In this blog, we’ll walk through a step-by step approach of deploying the Harbor VKS Standard Package in an air-gapped environment.
Below is the bill of Materials for the environment for this deployment
- VMware Cloud Foundation 9.0.2
- Supervisor Version v1.32.9
- vSphere Kubernetes Service 3.6.0+v1.35
- vSphere Kubernetes Runtime 1.35.0
- Bitnami Harbor
- Ubuntu 22.04 VM
Bitnami Harbor functions as the bootstrap container registry for storing and distributing VKS standard packages and vSphere Supervisor Services artifacts in this environment.
Provision a VKS Cluster for Harbor Deployment
- Connect to vSphere Supervisor using vcf cli
root@image-builder:/home/pj# vcf context create supervisor --endpoint 172.16.50.6 --username pj@workernode.lab --insecure-skip-tls-verify --auth-type basicProvide Password:Logged in successfully.You have access to the following contexts: supervisor supervisor:harbor-shared supervisor:opencost supervisor:svc-cci-ns-domain-c10 supervisor:svc-tkg-domain-c10 supervisor:svc-velero-domain-c10If the namespace context you wish to use is not in this list, you may need torefresh the context again, or contact your cluster administrator.To change context, use `vcf context use <context_name>`[ok] successfully saved context: supervisor[ok] successfully saved context: supervisor:svc-cci-ns-domain-c10[ok] successfully saved context: supervisor:opencost[ok] successfully saved context: supervisor:harbor-shared[ok] successfully saved context: supervisor:svc-tkg-domain-c10[ok] successfully saved context: supervisor:svc-velero-domain-c10
- Switch context to vSphere Namespace for VKS Cluster Deployment
root@image-builder:/home/pj# vcf context use supervisor:harbor-share[ok] Token is still active. Skipped the token refresh for context "supervisor:harbor-shared"[i] Successfully activated context 'supervisor:harbor-shared' (Type: kubernetes)[i] Fetching recommended plugins for active context 'supervisor:harbor-shared'...[ok] All recommended plugins are already installed and up-to-date.
- Retrieve Certificate for the BootStrap Registry and encode the certificate content with double-base64
echo | openssl s_client -connect bitnami.workernode.lab:443 | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > certificate.crtbase64 -w 0 certificate.crt | base64 -w 0
- Create a secret in vSphere Namespace for this registry
root@image-builder:/home/pj# cat harbor-shared-additional-ca-1.yamlapiVersion: v1data: additional-ca-1: TFMwdExTMUNSVWRKVGlCRFJWSlVTVVpKUTBGVVJTMHRMUzB0Q2sxSlNVZDNSRU5EUWt0cFowRjNTVUpCWjBsVVMxRkJRVUZCZVd0RlYyc3ZlRzU2ZUVaM1FVRkJRVUZCUkVSQlRrSm5hM0ZvYTJsSE9YY3dRa0ZSYzBZS1FVUkNUazFTVFhkRlVWbExRMXBKYldsYVVIbE1SMUZDUjFKWlJHSkhSbWxOVW05M1IwRlpTME5hU1cxcFdsQjVURWRSUWtkU1dVdGtNamw1WVRKV2VRcGliVGxyV2xSRllVMUNaMGRCTVZWRlFYaE5VbGxYVVhWa01qbDVZVEpXZVdKdE9XdGFVelZ6V1ZkSmQwaG9ZMDVOYWxsM1RXcEZlRTFxUVhkT1JFVjZDbGRvWTA1TmFtZDNUV3BGZUUxcVFYZE9SRVY2VjJwQ05FMVJjM2REVVZsRVZsRlJSMFYzU2twVWFrVlRUVUpCUjBFeFZVVkRRazFLVXpKR2VXSnRSakFLV1ZkMGFFMVNTWGRGUVZsRVZsRlJTRVYzYkVOYVZ6VnVXVmQ0TVdOdVZYaEZla0ZTUW1kT1ZrSkJiMVJEYkdSMlkyMTBiR050TlhaYVIxVjRRM3BCU2dwQ1owNVdRa0Z6VkVGcmJGVk5VamgzU0ZGWlJGWlJVVVJGZUZwcFlWaFNkVmxYTVhCTWJtUjJZMjEwYkdOdE5YWmFSMVYxWWtkR2FVMUpTVUpKYWtGT0NrSm5hM0ZvYTJsSE9YY3dRa0ZSUlVaQlFVOURRVkU0UVUxSlNVSkRaMHREUVZGRlFYbEJVbE5DZHpCWGFERm1RbTFSYmtJdlJqaFBaSGh6YjJoM1FrVUtaM1JLVHpoM1MwcHZMeXRpT0ZOcVJuSnRPVlJrTWpOUWNFWlRVa2hYZUc5WVJVdGpSa1ZVZWpkVFNsbGxRbVZyWW01dVpsWkxNRTFOVUV4TWJqRjFTUXA1TURWTmVsRjVTR1ZuVXpkM01uaE5NMFJoTkV0Wk4zb3djSGxoZGt0WU1ITmlUMlpxUkUxc1ZFRjZSR0Z0V2xSQ1JWcFRNV1o0YUVVMWFtWlJhMGRvQ2xaaFdteFNXbHBJY25GemRuSkpjRFJXWjFkTFVqTkhaMUp3VlcwdllraG9TbmhFZWtaR1ltbFpWVE5zV2tkQ0x6Z3ZUekZ4WTFOcmNXZzFiWE53VVc4S09VSlhRMVJ2V0cxWFZrZFhZMVZFVEVSbE1FZ3JRMVpCTmt0TFptODBaMVE1V2toNFR6QlBRak5zYlZoTlREUnRTQzgwWW1WVE1WUlpRWEJtVW1JM2FRbzJUSGgxWmtwcWMxSnNRMGx0U0hKQmFXWlJjM05uY25KNmFUaGpiRUpKV0VJNVNsbENlVUUxT1ZGdGMwNXBjVFFyUkVkSlVGVk1jVXhSU1VSQlVVRkNDbTgwU1VOaVJFTkRRVzFuZDAxQldVUldVakJTUWtOcmQwbzBZMFZ5UWtGTFRrbEpWMWx0YkRCaWJVWjBZVk0xTTJJelNuSmFXRXAxWWpKU2JFeHRlR2dLV1c5SlNGbHRiREJpYlVaMFlWUkJaRUpuVGxaSVVUUkZSbWRSVlhoWFZXbzFNSFIzY0ZNd2JuVlhVVGswTWtkU2QxUk1VVTB6WTNkSWQxbEVWbEl3YWdwQ1FtZDNSbTlCVlM5d1NUZzNVVE4yTldRM1VEbHZNR056WWpjdmFUbHZkV1l5UVhkbll6QkhRVEZWWkVoM1UwSjRWRU5DZDJwRFFuWTJRMEoyUzBOQ0NuVlpZVUowYlhocldWaEJOa3g1T0haUk1EUTVXVmRSZFdReU9YbGhNbFo1WW0wNWExcFROWE5aVjBselVUQTBPVmxYVVhOUk1EUTVVVEJTVVV4RlRrOEtVRlpDTVZsdGVIQlplVlY1VFVWMGJHVlRWWGxOUms1c1kyNWFjRmt5Vm5wTVJVNVBVRlpPYkdOdVduQlpNbFo2VEVWT1QxQlZUblppYlZwd1dqTldlUXBaV0ZKd1lqSTBjMUpGVFRsa01qbDVZVEpXZVdKdE9XdGFVM2hGVVhveGMxbFhTUzlaTWxaNVpFZHNiV0ZYVG1oa1IxWlRXbGhhZGxreVJqQmhWemwxQ2xSSGJIcGtSRGxwV1ZoT2JGQXlPV2xoYlZacVpFVk9jMWxZVG5wUVYwNVRWRVZTY0dNelVubGhWMG94WkVkc2RtSnNRblpoVnpVd1RVbElSMEpuWjNJS1FtZEZSa0pSWTBKQlVWTkNkVlJEUW5ScVEwSnpkMWxKUzNkWlFrSlJWVWhOUVV0SFoyRmFjMXBIUm5kUGFUaDJUREJPVDFCWFJtdE1ibVIyWTIxMGJBcGpiVFYyV2tkVmRXSkhSbWxNUlU1UFVGVkdTbEZUZUVSVWFqRlJaRmRLYzJGWFRXeE5ha0pNV2xocmJFMXFRbFJhV0VveVlWZE9iR041ZUVSVWFqRlVDbHBZU2pKaFYwNXNZM2w0UkZScU1VUmlNalZ0WVZka01XTnRSakJoVnpsMVRFVlNSRkJZWkhaamJYUnNZMjAxZGxwSFZYTlNSVTA1WWtkR2FWQXlUa0lLVVRKV2VXUkhiRzFoVjA1b1pFZFZMMWx0Um5wYVZEbDJXVzF3YkZrelVrUmlSMFo2WTNveGFscFlTakJoVjFwd1dUSkdNR0ZYT1hWUldGWXdZVWM1ZVFwaFdGSTFUVUYzUjBFeFZXUkZkMFZDTDNkUlEwMUJRWGRFWjFsRVZsSXdVRUZSU0M5Q1FWRkVRV2RZWjAxRU1FZERVM05IUVZGUlFtZHFZMVpDZDFGM0NrMURORWRLYVhOSFFWRlJRbWRxWTFaRFNXWm1lR2w1UkN0alp6Tm9aVWRHUVVsTWFXMVdVMFpxT1VwR1V6UlBjU3RFTWtjMlRUVkhRV2RHYTBGblJVVUtUVUV3UjBOVGNVZFRTV0l6UkZGRlFrTjNWVUZCTkVsRFFWRkJlblJwVFhoU1ZEWnBaMnN4WTFwUGFERk1VMWgzU25WelRXb3lPRWw2ZURRMFFrUmlUd3BOUWtoTk1VWmtNbVJGVjNWbE5tMVRNVzVDYVN0dlpXbFZZbEV4WW1JNFRsRkdXV2RrVEhWdFRrSjFjakJNTTNGelVubFRNbFJpVVZFeGVraFFkVU5pQ2xZMU1VVjJlbGRpVDJSNGJYUTVlR2cyTm0xclRHZEhTbWh5V2pod1oyOW5ZbGRWVGpWUkx6bDJVREo1VDI5clpIQk1iRTFxT0ZwaVR5OXVaMk5rV0RnS1psWkZNVVpTU0RORFZscHRSMVl5TVRWb1RqSjNhSE51TkZWeVFVMDRNMnd4U21JelNGb3pZM2hzU3k5MFUzUlBPVFp3Y0RGUWFuZFdWMDFTTjAxTk13cGhkRUozZFRkRWJVNXJTR05rU1RSVE1HVlZjRlF6YUdsemNHVk9jVGN4YzI1RmNHMW1jMGRwZGxaTFRXMUhkMVJTT0ZwS2NFOXBUbHB3U1UxbmRHVnpDbFZ1VlhkalJsYzNhMVZsZFhFelJUQktlV2xVVTI0dk1tbDZkRFJWYW5wNWMwWTBWRkowYkZvMFIyMWxia2g1WkZCb2RYbEhObEZ5UlZCT1JXNUVlVGtLZG1KV2RYSXpLMkpUWVUxQmRWZ3ZibEpLYVRaaVdVNXBlalkwYVVwTGNsaGpTR2hSY1dsSFdHRkJWR3ROYkVZM01Fa3pRMEpTV0ZWa1RYZE9kVUo0UWdwa2NGbHpRWHBVYUd4TVMwSlZReTlCVlU4MVV6aHdlRkJPWVdscFZ6WmlXRVpCTW5kak5WRm1Va2xpVjBWMmRYSXJWMHd4Ym14R1UyMU5UMHB2WWt4T0NuZHhjSFJQUWxOVGVHOW1aVE5YV1Uxd1VHcEthRVpHZDA1NmIycHRhVEYzWkZwa1dHWTRSVnAyWWtoc1YwUkpka2hVYVVNM1RFTmhlVVJ2ZDJack5Xd0tZbmhvTWpJNE16UlZTRzlxVW1VMWNFOXJiM2xNVUdab2VFMWlNWEJYWkZGSk5WbzJPWEpMVDJkU2EzaDFNREIwVVRCcFV6WnFkSE5aWVRoMVJrTm5lQW9yTlRoVVJHTkRWMVpaUjFsSWRIbFBSRXhvVkZwcU9VeHNSRVJVUkhSSVRUUlRhVE0yVm10Q2NFcDRWRlJPTm5WcUsyZHlRa040WTNJM1oycHhXSGRDQ2sxTWNFNHdVVDA5Q2kwdExTMHRSVTVFSUVORlVsUkpSa2xEUVZSRkxTMHRMUzBLkind: Secretmetadata: name: harbor-cluster-1-user-trusted-ca-secret namespace: harbor-sharedtype: Opaqueroot@image-builder:/home/pj# kubectl apply -f harbor-shared-additional-ca-1.yamlsecret/harbor-cluster-1-user-trusted-ca-secret createdroot@image-builder:/home/pj# kubectl get secretsNAME TYPE DATA AGEharbor-cluster-1-user-trusted-ca-secret Opaque 1 3s
- Create the VKS cluster by providing the created secret in cluster deploytment yaml under additionalTrustedCAs section with secret & key name. Below is the YAML file used to create the VKS cluster. The cluster has 3 Control Plane node with 2vCPU/4 GB RAM and 3 Worker Node with 4 vCPU and 16GB RAM.
root@image-builder:/home/pj# cat harbor-shared-cluster.yamlapiVersion: cluster.x-k8s.io/v1beta2kind: Clustermetadata: name: harbor-cluster-1 namespace: harbor-sharedspec: clusterNetwork: pods: cidrBlocks: - 192.168.156.0/20 services: cidrBlocks: - 10.96.0.0/12 serviceDomain: cluster.local topology: classRef: name: builtin-generic-v3.6.0 namespace: vmware-system-vks-public version: v1.35.0---vmware.2-vkr.4 variables: - name: vsphereOptions value: persistentVolumes: defaultStorageClass: k8s-nfs-policy - name: kubernetes value: certificateRotation: enabled: true renewalDaysBeforeExpiry: 90 security: podSecurityStandard: audit: restricted auditVersion: latest enforce: privileged enforceVersion: latest warn: privileged warnVersion: latest - name: osConfiguration value: ntp: servers: - 172.16.9.1 value: trust: additionalTrustedCAs: - caCert: secretRef: key: "additional-ca-1" name: "harbor-cluster-1-user-trusted-ca-secret" - name: vmClass value: guaranteed-small - name: storageClass value: k8s-nfs-policy controlPlane: replicas: 3 metadata: annotations: run.tanzu.vmware.com/resolve-os-image: os-name=ubuntu, content-library=cl-da827350a6aac5167, os-version=24.04 workers: machineDeployments: - class: node-pool name: costly-cluster-1-np-l3xl replicas: 3 metadata: annotations: run.tanzu.vmware.com/resolve-os-image: os-name=ubuntu, content-library=cl-da827350a6aac5167, os-version=24.04 variables: overrides: - name: vmClass value: best-effort-large - name: volumes value: - name: containerd-harbor-cluster-1 mountPath: /var/lib/containerd storageClass: k8s-nfs-policy capacity: 20Gi - name: kubelet-harbor-cluster-1 mountPath: /var/lib/kubelet storageClass: k8s-nfs-policy capacity: 20Giroot@image-builder:/home/pj# kubectl apply -f harbor-shared-cluster.yamlcluster.cluster.x-k8s.io/harbor-cluster-1 created
- Wait for the cluster creation to finish and verify the cluster status
root@image-builder:/home/pj# kubectl gt clusters -n harbor-sharedNAME CLUSTERCLASS AVAILABLE CP DESIRED CP AVAILABLE CP UP-TO-DATE W DESIRED W AVAILABLE W UP-TO-DATE PHASE AGE VERSIONharbor-cluster-1 builtin-generic-v3.6.0 True 3 3 3 3 3 3 Provisioned 27m v1.35.0+vmware.2
Download and Upload VKS Standard Packages to Bootstrap Registry
- Download vcf cli v9.0.2 from Broadcom Repository
- Install vcf cli on the Ubuntu Machine
root@image-builder:/home/pj# tar -zxf vcf-cli.tar.gzroot@image-builder:/home/pj# ls -latrh | grep -i vcf-cli-rwxr-xr-x 1 501 staff 145M Feb 3 00:04 vcf-cli-linux_amd64-rwxr-xr-x 1 501 staff 163 Feb 3 00:04 ._vcf-cli-linux_amd64-rw-r--r-- 1 root root 44M Feb 18 23:49 vcf-cli.tar.gzroot@image-builder:/home/pj# sudo install vcf-cli-linux_amd64 /usr/local/bin/vcf
- Install imgpkg plugin for vcf cli
root@image-builder:/home/pj# vcf plugin install imgpkg[i] Installed plugin 'imgpkg:v9.0.2'[ok] successfully installed 'imgpkg' pluginroot@image-builder:/home/pj# vcf plugin list NAME DESCRIPTION INSTALLED STATUS imgpkg package, distribute, and relocate your configuration and dependent oci images as v9.0.2 installed one oci artifact telemetry Telemetry for VCF Workload CLI v9.0.1 installed
- Download VKS Standard Packages as a Tar Bundle using vcf cli . The bundle size is 8.8 Gb and can take some time to download.
root@image-builder:/home/pj# vcf imgpkg copy -b projects.packages.broadcom.com/vsphere/supervisor/vks-standard-packages/3.6.0-20260320/vks-standard-packages:3.6.0-20260320 --to-tar /home/pj/vks-standard-packages.tar --cosign-signaturescopy | exporting 241 images...
- Login to Bitnami Harbor
root@image-builder:/# docker login bitnami.workernode.labUsername: adminPassword:WARNING! Your credentials are stored unencrypted in '/root/.docker/config.json'.Configure a credential helper to remove this warning. Seehttps://docs.docker.com/go/credential-store/Login Succeeded
- Upload the VKS Standard Package Image Tar Bundle to Bitnami Harbor which is being used as a Bootstrap Registry in this environment
root@image-builder:/home/pj# vcf imgpkg copy --tar /home/pj/vks-standard-packages.tar --to-repo bitnami.workernode.lab/vks-standard-packages/v3.6.0 --registry-ca-cert-path /etc/docker/certs.d/bitnami.workernode.lab/ca.crt --cosign-signaturescopy | importing 241 images...copy | Tagging images
Configure Package Repository on VKS Cluster
- Login to VKS Cluster using vcf cli
root@image-builder:/home/pj# vcf context create harbor-cluster --endpoint 172.16.50.6 --insecure-skip-tls-verify --workload-cluster-name harbor-cluster-1 --workload-cluster-namespace harbor-shared --usernam e pj@workernode.labProvide Password:[i] Logging in to Kubernetes cluster (harbor-cluster-1) (harbor-shared)[i] Successfully logged in to Kubernetes cluster 172.16.50.10You have access to the following contexts: harbor-cluster harbor-cluster:harbor-cluster-1If the namespace context you wish to use is not in this list, you may need torefresh the context again, or contact your cluster administrator.To change context, use `vcf context use <context_name>`[ok] successfully saved context: harbor-cluster[ok] successfully saved context: harbor-cluster:harbor-cluster-1root@image-builder:/home/pj# vcf context use harbor-cluster:harbor-cluster-1[ok] Token is still active. Skipped the token refresh for context "harbor-cluster:harbor-cluster-1"[i] Successfully activated context 'harbor-cluster:harbor-cluster-1' (Type: kubernetes)[i] Fetching recommended plugins for active context 'harbor-cluster:harbor-cluster-1'...[ok] No recommended plugins found.
- Add the Package Repository to VKS Cluster
root@image-builder:/home/pj# vcf package repository add standard-package-repo --url bitnami.workernode.lab/vks-standard-packages/v3.6.0:3.6.0-20260320 -n tkg-system1:46:14PM: Updating package repository resource 'standard-package-repo' in namespace 'tkg-system'1:46:14PM: Waiting for package repository reconciliation for 'standard-package-repo'1:46:14PM: Fetch started1:46:14PM: Fetching | apiVersion: vendir.k14s.io/v1alpha1 | directories: | - contents: | - imgpkgBundle: | image: bitnami.workernode.lab/vks-standard-packages/v3.6.0@sha256:c0d048b29156b19431591186bcc8edbc366941e77b89e53f4b2e70d05a6ad080 | tag: 3.6.0-20260320 | path: . | path: "0" | kind: LockConfig |1:46:14PM: Fetch succeeded1:46:15PM: Template succeeded1:46:15PM: Deploy started (2s ago)1:46:16PM: Deploying (1s ago) | Target cluster 'https://10.96.0.1:443' | Changes | Namespace Name Kind Age Op Op st. Wait to Rs Ri | tkg-system ako.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ ako.kubernetes.vmware.com.1.13.4+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ ako.kubernetes.vmware.com.2.1.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ ako.kubernetes.vmware.com.2.1.3+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cert-manager.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ cert-manager.kubernetes.vmware.com.1.18.2+vmware.2-vks.2 Package - create fallback on update or noop - - - | ^ cert-manager.kubernetes.vmware.com.1.18.3+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cert-manager.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cert-manager.kubernetes.vmware.com.1.19.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cilium.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ cilium.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.31.3+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.32.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.34.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.34.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ cluster-autoscaler.kubernetes.vmware.com.1.35.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ contour.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ contour.kubernetes.vmware.com.1.32.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ contour.kubernetes.vmware.com.1.33.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ contour.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ contour.kubernetes.vmware.com.1.33.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ external-dns.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ external-dns.kubernetes.vmware.com.0.18.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ external-dns.kubernetes.vmware.com.0.18.0+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ external-dns.kubernetes.vmware.com.0.20.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ fluent-bit.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ fluent-bit.kubernetes.vmware.com.4.0.8+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ fluent-bit.kubernetes.vmware.com.4.0.8+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ fluent-bit.kubernetes.vmware.com.4.1.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ fluent-bit.kubernetes.vmware.com.4.2.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com.2.13.5+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com.2.14.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com.2.14.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com.2.14.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ harbor.kubernetes.vmware.com.2.14.3+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ istio.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ istio.kubernetes.vmware.com.1.27.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ istio.kubernetes.vmware.com.1.27.4+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ istio.kubernetes.vmware.com.1.27.5+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ istio.kubernetes.vmware.com.1.28.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ prometheus.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ prometheus.kubernetes.vmware.com.3.5.0+vmware.1-vks.2 Package - create fallback on update or noop - - - | ^ prometheus.kubernetes.vmware.com.3.5.0+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ prometheus.kubernetes.vmware.com.3.5.0+vmware.3-vks.1 Package - create fallback on update or noop - - - | ^ sriov-network-device-plugin.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.3-vks.1 Package - create fallback on update or noop - - - | ^ sriov-network-device-plugin.kubernetes.vmware.com.3.11.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ telegraf.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ telegraf.kubernetes.vmware.com.1.35.4+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ telegraf.kubernetes.vmware.com.1.35.4+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ telegraf.kubernetes.vmware.com.1.36.4+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ telegraf.kubernetes.vmware.com.1.37.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ vault-injector.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ vault-injector.kubernetes.vmware.com.1.6.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com.1.16.2+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com.1.16.2+vmware.3-vks.1 Package - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com.1.17.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com.1.17.1+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ velero.kubernetes.vmware.com.1.17.2+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ vsphere-pv-csi-webhook.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.2-vks.1 Package - create fallback on update or noop - - - | ^ vsphere-pv-csi-webhook.kubernetes.vmware.com.3.7.0+vmware.1-vks.1 Package - create fallback on update or noop - - - | ^ windows-gmsa-webhook.kubernetes.vmware.com PackageMetadata - create fallback on update or noop - - - | ^ windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.3-vks.1 Package - create fallback on update or noop - - - | ^ windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.4-vks.1 Package - create fallback on update or noop - - - | ^ windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.5-vks.1 Package - create fallback on update or noop - - - | Op: 72 create, 0 delete, 0 update, 0 noop, 0 exists | Wait to: 0 reconcile, 0 delete, 72 noop | 8:16:15AM: ---- applying 72 changes [0/72 done] ---- | 8:16:15AM: create packagemetadata/windows-gmsa-webhook.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create packagemetadata/harbor.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/harbor.kubernetes.vmware.com.2.14.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/istio.kubernetes.vmware.com.1.27.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/harbor.kubernetes.vmware.com.2.14.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/istio.kubernetes.vmware.com.1.27.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/istio.kubernetes.vmware.com.1.27.5+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create packagemetadata/istio.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/istio.kubernetes.vmware.com.1.28.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/prometheus.kubernetes.vmware.com.3.5.0+vmware.1-vks.2 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create package/prometheus.kubernetes.vmware.com.3.5.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:15AM: create packagemetadata/prometheus.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/sriov-network-device-plugin.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/sriov-network-device-plugin.kubernetes.vmware.com.3.11.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/telegraf.kubernetes.vmware.com.1.35.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/prometheus.kubernetes.vmware.com.3.5.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/telegraf.kubernetes.vmware.com.1.35.4+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/telegraf.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/telegraf.kubernetes.vmware.com.1.36.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/telegraf.kubernetes.vmware.com.1.37.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/velero.kubernetes.vmware.com.1.16.2+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/vault-injector.kubernetes.vmware.com.1.6.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/vault-injector.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/velero.kubernetes.vmware.com.1.16.2+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/velero.kubernetes.vmware.com.1.17.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/velero.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/velero.kubernetes.vmware.com.1.17.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/vsphere-pv-csi-webhook.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/velero.kubernetes.vmware.com.1.17.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/cluster-autoscaler.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.4-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.5-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.7.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/ako.kubernetes.vmware.com.1.13.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/ako.kubernetes.vmware.com.2.1.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cert-manager.kubernetes.vmware.com.1.18.2+vmware.2-vks.2 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cert-manager.kubernetes.vmware.com.1.18.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cert-manager.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/ako.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/ako.kubernetes.vmware.com.2.1.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cilium.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cert-manager.kubernetes.vmware.com.1.19.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/cilium.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/cert-manager.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.31.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.32.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.34.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.34.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/cluster-autoscaler.kubernetes.vmware.com.1.35.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/external-dns.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/contour.kubernetes.vmware.com.1.32.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/contour.kubernetes.vmware.com.1.33.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/contour.kubernetes.vmware.com.1.33.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/contour.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/contour.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/external-dns.kubernetes.vmware.com.0.18.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/external-dns.kubernetes.vmware.com.0.18.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/external-dns.kubernetes.vmware.com.0.20.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/fluent-bit.kubernetes.vmware.com.4.2.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/fluent-bit.kubernetes.vmware.com.4.0.8+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/fluent-bit.kubernetes.vmware.com.4.0.8+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/fluent-bit.kubernetes.vmware.com.4.1.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/harbor.kubernetes.vmware.com.2.13.5+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create packagemetadata/fluent-bit.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/harbor.kubernetes.vmware.com.2.14.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: create package/harbor.kubernetes.vmware.com.2.14.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ---- waiting on 72 changes [0/72 done] ---- | 8:16:16AM: ok: noop package/prometheus.kubernetes.vmware.com.3.5.0+vmware.1-vks.2 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/windows-gmsa-webhook.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/harbor.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/harbor.kubernetes.vmware.com.2.14.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/istio.kubernetes.vmware.com.1.27.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/harbor.kubernetes.vmware.com.2.14.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/istio.kubernetes.vmware.com.1.27.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/istio.kubernetes.vmware.com.1.27.5+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/istio.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/istio.kubernetes.vmware.com.1.28.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cert-manager.kubernetes.vmware.com.1.18.2+vmware.2-vks.2 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/prometheus.kubernetes.vmware.com.3.5.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/prometheus.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/sriov-network-device-plugin.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/sriov-network-device-plugin.kubernetes.vmware.com.3.10.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/sriov-network-device-plugin.kubernetes.vmware.com.3.11.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/telegraf.kubernetes.vmware.com.1.35.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/prometheus.kubernetes.vmware.com.3.5.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/telegraf.kubernetes.vmware.com.1.35.4+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/telegraf.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/telegraf.kubernetes.vmware.com.1.36.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/telegraf.kubernetes.vmware.com.1.37.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/velero.kubernetes.vmware.com.1.16.2+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/vault-injector.kubernetes.vmware.com.1.6.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/vault-injector.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/velero.kubernetes.vmware.com.1.16.2+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/velero.kubernetes.vmware.com.1.17.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/velero.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/velero.kubernetes.vmware.com.1.17.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.6.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/vsphere-pv-csi-webhook.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/velero.kubernetes.vmware.com.1.17.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/cluster-autoscaler.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.4-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.5-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/vsphere-pv-csi-webhook.kubernetes.vmware.com.3.7.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/windows-gmsa-webhook.kubernetes.vmware.com.0.13.0+vmware.3-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/ako.kubernetes.vmware.com.1.13.4+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/ako.kubernetes.vmware.com.2.1.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/external-dns.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cert-manager.kubernetes.vmware.com.1.18.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cert-manager.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/ako.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/ako.kubernetes.vmware.com.2.1.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cilium.kubernetes.vmware.com.1.19.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cert-manager.kubernetes.vmware.com.1.19.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/cilium.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/cert-manager.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.31.3+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.32.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.34.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.34.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/cluster-autoscaler.kubernetes.vmware.com.1.35.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/external-dns.kubernetes.vmware.com.0.20.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/contour.kubernetes.vmware.com.1.32.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/contour.kubernetes.vmware.com.1.33.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/contour.kubernetes.vmware.com.1.33.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/contour.kubernetes.vmware.com.1.33.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/contour.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/external-dns.kubernetes.vmware.com.0.18.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/external-dns.kubernetes.vmware.com.0.18.0+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/fluent-bit.kubernetes.vmware.com.4.1.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/fluent-bit.kubernetes.vmware.com.4.2.2+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/fluent-bit.kubernetes.vmware.com.4.0.8+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/fluent-bit.kubernetes.vmware.com.4.0.8+vmware.2-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop packagemetadata/fluent-bit.kubernetes.vmware.com (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/harbor.kubernetes.vmware.com.2.13.5+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/harbor.kubernetes.vmware.com.2.14.0+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ok: noop package/harbor.kubernetes.vmware.com.2.14.1+vmware.1-vks.1 (data.packaging.carvel.dev/v1alpha1) namespace: tkg-system | 8:16:16AM: ---- applying complete [72/72 done] ---- | 8:16:16AM: ---- waiting complete [72/72 done] ---- | Succeeded1:46:16PM: Deploy succeeded (1s ago)
- Verify available Harbor Packages in the repository
root@image-builder:/home/pj# vcf package available get harbor.kubernetes.vmware.com -n tkg-system NAME: harbor.kubernetes.vmware.com DISPLAY-NAME: Harbor CATEGORIES: - OCI registry SHORT-DESCRIPTION: OCI Registry LONG-DESCRIPTION: Harbor is an open source trusted cloud native registry project that stores,signs, and scans content. Harbor extends the open source Docker Distribution byadding the functionalities usually required by users such as security, identityand management. PROVIDER: VMware MAINTAINERS: - name: Miner Yang SUPPORT-DESCRIPTION: https://goharbor.io VERSION RELEASED-AT 2.13.5+vmware.1-vks.1 2026-03-10 22:00:00 +0530 IST 2.14.0+vmware.1-vks.1 2025-10-10 23:00:00 +0530 IST 2.14.1+vmware.1-vks.1 2025-12-24 00:00:00 +0530 IST 2.14.2+vmware.1-vks.1 2026-02-05 17:00:00 +0530 IST 2.14.3+vmware.1-vks.1 2026-03-10 21:00:00 +0530 IS
Verify Cert-manager and Contour Packages in the repository as they are a pre-requisite for Harbor Deployment.
root@image-builder:/home/pj# vcf package available get cert-manager.kubernetes.vmware.com -n tkg-system NAME: cert-manager.kubernetes.vmware.com DISPLAY-NAME: cert-manager CATEGORIES: - certificate management SHORT-DESCRIPTION: Certificate management LONG-DESCRIPTION: Provides certificate management provisioning within the cluster PROVIDER: VMware MAINTAINERS: - name: Chao Yu SUPPORT-DESCRIPTION: Go to https://cert-manager.io/ for documentation or the #cert-manager channel onKubernetes slack VERSION RELEASED-AT 1.18.2+vmware.2-vks.2 2025-10-22 17:30:00 +0530 IST 1.18.3+vmware.1-vks.1 2025-12-18 17:30:00 +0530 IST 1.19.1+vmware.1-vks.1 2025-12-18 17:30:00 +0530 IST 1.19.2+vmware.1-vks.1 2026-02-11 17:30:00 +0530 ISTroot@image-builder:/home/pj# vcf package available get contour.kubernetes.vmware.com -n tkg-system NAME: contour.kubernetes.vmware.com DISPLAY-NAME: contour CATEGORIES: - ingress- envoy- contour SHORT-DESCRIPTION: An ingress controller LONG-DESCRIPTION: An Envoy-based ingress controller that supports dynamic configuration updatesand multi-team ingress delegation. See https://projectcontour.io for moreinformation. PROVIDER: VMware MAINTAINERS: - name: Bei Hou- name: Chuan Mi SUPPORT-DESCRIPTION: Go to https://projectcontour.io for documentation or the #contour channel onKubernetes slack VERSION RELEASED-AT 1.32.0+vmware.1-vks.1 2025-08-19 05:30:00 +0530 IST 1.33.0+vmware.1-vks.1 2025-10-22 05:30:00 +0530 IST 1.33.0+vmware.2-vks.1 2025-12-18 05:30:00 +0530 IST 1.33.1+vmware.1-vks.1 2026-02-11 05:30:00 +0530 IST
Prior to installing Harbor , we would have to install cert-manager and contour package which are pre-requisites for Harbor Deployment
Deployment of Cert Manager on VKS Cluster
- Create a namespace for Cert Manager PackageInstall resource . The namespace name cannot be cert-manager as Cert Manager package creates a namespace named cert-manager to save related resources
root@image-builder:/home/pj# kubectl create ns package-installednamespace/package-installed created
- Generate Cert-Manager values.yaml file
root@image-builder:/home/pj# vcf package available get cert-manager.kubernetes.vmware.com/1.19.2+vmware.1-vks.1 --default-values-file-output cert-manager-values.yamlCreated default values file at cert-manager-values.yaml NAME: cert-manager.kubernetes.vmware.com DISPLAY-NAME: cert-manager CATEGORIES: - certificate management SHORT-DESCRIPTION: Certificate management LONG-DESCRIPTION: Provides certificate management provisioning within the cluster PROVIDER: VMware MAINTAINERS: - name: Chao Yu SUPPORT-DESCRIPTION: Go to https://cert-manager.io/ for documentation or the #cert-manager channel onKubernetes slack VERSION: 1.19.2+vmware.1-vks.1 RELEASED-AT: 2026-02-11 17:30:00 +0530 IST MIN-CAPACITY-REQUIREMENTS: Varies significantly based on number of Certificate objects RELEASE-NOTES: cert-manager 1.19.2https://github.com/jetstack/cert-manager/releases/tag/v1.19.2 LICENSES: VMware's End User License Agreement (Underlying OSS license: Apache License 2.0)root@image-builder:/home/pj#
- Install Cert Manager packages with default options
root@image-builder:/home/pj# vcf package install cert-manager -p cert-manager.kubernetes.vmware.com --namespace package-installed --version 1.19.2+vmware.1-vks.14:14:16PM: Creating service account 'cert-manager-package-installed-sa'4:14:16PM: Creating cluster admin role 'cert-manager-package-installed-cluster-role'4:14:16PM: Creating cluster role binding 'cert-manager-package-installed-cluster-rolebinding'4:14:16PM: Creating package install resource4:14:16PM: Waiting for PackageInstall reconciliation for 'cert-manager'4:14:16PM: Fetch started4:14:16PM: Fetching | apiVersion: vendir.k14s.io/v1alpha1 | directories: | - contents: | - imgpkgBundle: | image: bitnami.workernode.lab/vks-standard-packages/v3.6.0@sha256:cdd5a7fd4d5d714026b6a2a811d9e5bf31ac89a44837fb42a40b7f80d6d1af7b | path: . | path: "0" | kind: LockConfig |4:14:16PM: Fetch succeeded4:14:17PM: Template succeeded4:14:17PM: Deploy started (2s ago)4:14:19PM: Deploying | Target cluster 'https://10.96.0.1:443' (nodes: harbor-cluster-1-xfzhx-lwf7l, 5+)>>>>>>>>>>>> | 10:44:27AM: L ok: waiting on replicaset/cert-manager-webhook-74849cf594 (apps/v1) namespace: cert-manager | 10:44:27AM: L ongoing: waiting on pod/cert-manager-webhook-74849cf594-rs8bg (v1) namespace: cert-manager | 10:44:27AM: ^ Condition Ready is not True (False) | 10:44:27AM: ok: reconcile deployment/cert-manager (apps/v1) namespace: cert-manager | 10:44:27AM: ---- waiting on 1 changes [52/53 done] ----4:14:33PM: Deploy succeeded
- Validate Package Installation
root@image-builder:/home/pj# vcf package installed list -n package-installed NAME PACKAGE-NAME PACKAGE-VERSION STATUS cert-manager cert-manager.kubernetes.vmware.com 1.19.2+vmware.1-vks.1 Reconcile succeededroot@image-builder:/home/pj# kubectl get all -n cert-managerNAME READY STATUS RESTARTS AGEpod/cert-manager-5687cbdb4c-rxdmk 1/1 Running 0 2m19spod/cert-manager-cainjector-85cddc576b-v9h67 1/1 Running 0 2m20spod/cert-manager-webhook-74849cf594-rs8bg 1/1 Running 0 2m20sNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEservice/cert-manager ClusterIP 10.109.94.50 <none> 9402/TCP 2m20sservice/cert-manager-cainjector ClusterIP 10.110.132.104 <none> 9402/TCP 2m20sservice/cert-manager-webhook ClusterIP 10.100.128.3 <none> 443/TCP,9402/TCP 2m20sNAME READY UP-TO-DATE AVAILABLE AGEdeployment.apps/cert-manager 1/1 1 1 2m19sdeployment.apps/cert-manager-cainjector 1/1 1 1 2m20sdeployment.apps/cert-manager-webhook 1/1 1 1 2m20sNAME DESIRED CURRENT READY AGEreplicaset.apps/cert-manager-5687cbdb4c 1 1 1 2m19sreplicaset.apps/cert-manager-cainjector-85cddc576b 1 1 1 2m20sreplicaset.apps/cert-manager-webhook-74849cf594 1 1 1 2m20s
Deployment of Contour on VKS Cluster
- Generate the contour-default-values.yaml file
root@image-builder:/home/pj# vcf package available get contour.kubernetes.vmware.com/1.33.1+vmware.1-vks.1 --default-values-file-output contour-data-values.yaml -n tkg-systemCreated default values file at contour-data-values.yaml NAME: contour.kubernetes.vmware.com DISPLAY-NAME: contour CATEGORIES: - ingress- envoy- contour SHORT-DESCRIPTION: An ingress controller LONG-DESCRIPTION: An Envoy-based ingress controller that supports dynamic configuration updatesand multi-team ingress delegation. See https://projectcontour.io for moreinformation. PROVIDER: VMware MAINTAINERS: - name: Bei Hou- name: Chuan Mi SUPPORT-DESCRIPTION: Go to https://projectcontour.io for documentation or the #contour channel onKubernetes slack VERSION: 1.33.1+vmware.1-vks.1 RELEASED-AT: 2026-02-11 05:30:00 +0530 IST MIN-CAPACITY-REQUIREMENTS: Varies significantly based on number of Services, Ingresses/HTTPProxies, etc. Astarting point is 128MB RAM and 0.5 CPU for each Contour and Envoy pod, but thiscan and should be tuned based on observed usage. RELEASE-NOTES: contour 1.33.1 https://github.com/projectcontour/contour/releases/tag/v1.33.1 LICENSES: VMware's End User License Agreement (Underlying OSS license: Apache License 2.0)
- Edit the contour-data-values.yaml file and configure the Envoy service type as LoadBalancer to enable external access to Kubernetes services. Refer to the example below for guidance.
root@image-builder:/home/pj# cat infrastructure_provider: vspherenamespace: tanzu-system-ingresscontour: configFileContents: {} useProxyProtocol: false replicas: 2 pspNames: "vmware-system-restricted" logLevel: infoenvoy: service: type: LoadBalancer annotations: {} externalTrafficPolicy: Cluster disableWait: false hostPorts: enable: true http: 80 https: 443 hostNetwork: false terminationGracePeriodSeconds: 300 logLevel: infocertificates: caDuration: 8760h caRenewBefore: 720h leafDuration: 720h leafRenewBefore: 360h
- Create a namespace for contour package
root@image-builder:/home/pj# kubectl create ns contournamespace/contour created
- Install Contour with the edited contour-data-values.yaml
root@image-builder:/home/pj# vcf package install contour -p contour.kubernetes.vmware.com -v 1.33.1+vmware.1-vks.1 --values-file contour-data-values.yaml -n contour4:26:05PM: Creating service account 'contour-contour-sa'4:26:05PM: Creating cluster admin role 'contour-contour-cluster-role'4:26:05PM: Creating cluster role binding 'contour-contour-cluster-rolebinding'4:26:05PM: Creating secret 'contour-contour-values'4:26:05PM: Creating package install resource4:26:05PM: Waiting for PackageInstall reconciliation for 'contour'4:26:05PM: Fetch started (1s ago)4:26:06PM: Fetching | apiVersion: vendir.k14s.io/v1alpha1 | directories: | - contents: | - imgpkgBundle: | image: bitnami.workernode.lab/vks-standard-packages/v3.6.0@sha256:0524a083978c99d88c70fec8a2edd188c6b294d582774c11be065c4deaed8425 | path: . | path: "0" | kind: LockConfig |4:26:06PM: Fetch succeeded4:26:06PM: Template succeeded4:26:06PM: Deploy started (2s ago)4:26:08PM: Deploying | Target cluster 'https://10.96.0.1:443' (nodes: harbor-cluster-1-xfzhx-lwf7l, 5+)>>>>>>>>>>>> | 10:56:24AM: ---- waiting on 1 changes [26/27 done] ---- | 10:56:33AM: ok: reconcile service/envoy (v1) namespace: tanzu-system-ingress | 10:56:33AM: ---- applying complete [27/27 done] ---- | 10:56:33AM: ---- waiting complete [27/27 done] ---- | Succeeded4:26:33PM: Deploy succeeded
- Validate Package Installation
root@image-builder:/home/pj# vcf package installed list -n contour NAME PACKAGE-NAME PACKAGE-VERSION STATUS contour contour.kubernetes.vmware.com 1.33.1+vmware.1-vks.1 Reconcile succeededroot@image-builder:/home/pj# kubectl -n tanzu-system-ingress get allNAME READY STATUS RESTARTS AGEpod/contour-76485dbd95-77js4 1/1 Running 0 63spod/contour-76485dbd95-qmmp7 1/1 Running 0 63spod/envoy-27fqm 2/2 Running 0 63spod/envoy-djsfv 2/2 Running 0 63spod/envoy-qb2z5 2/2 Running 0 63sNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEservice/contour ClusterIP 10.111.13.227 <none> 8001/TCP 64sservice/envoy LoadBalancer 10.101.112.187 172.16.50.11 80:30972/TCP,443:30301/TCP 63sNAME DESIRED CURRENT READY UP-TO-DATE AVAILABLE NODE SELECTOR AGEdaemonset.apps/envoy 3 3 3 3 3 <none> 64sNAME READY UP-TO-DATE AVAILABLE AGEdeployment.apps/contour 2/2 2 2 63sNAME DESIRED CURRENT READY AGEreplicaset.apps/contour-76485dbd95 2 2 2 63s
Deployment of Harbor on VKS Cluster
Generate harbor-data-values.yaml for Harbor Installation
root@image-builder:/home/pj# vcf package available get harbor.kubernetes.vmware.com/2.14.3+vmware.1-vks.1 --default-values-file-output harbor-data-values.yamlCreated default values file at harbor-data-values.yaml NAME: harbor.kubernetes.vmware.com DISPLAY-NAME: Harbor CATEGORIES: - OCI registry SHORT-DESCRIPTION: OCI Registry LONG-DESCRIPTION: Harbor is an open source trusted cloud native registry project that stores,signs, and scans content. Harbor extends the open source Docker Distribution byadding the functionalities usually required by users such as security, identityand management. PROVIDER: VMware MAINTAINERS: - name: Miner Yang SUPPORT-DESCRIPTION: https://goharbor.io VERSION: 2.14.3+vmware.1-vks.1 RELEASED-AT: 2026-03-10 21:00:00 +0530 IST MIN-CAPACITY-REQUIREMENTS: RELEASE-NOTES: harbor v2.14.3 https://github.com/goharbor/harbor/releases/tag/v2.14.3 LICENSES: Apache 2.0
- Edit the harbor-data-values.yaml file and update the required values for the mandatory parameters per the product documentation. The harbor-data-values.yaml should be as below
cache:
enabled: false
expireHours: 24
concurrentRequestLimit:
registry:
enabled: false
max: 500
core:
replicas: 1
secret: "a7f3K9mP2xQ8vL1z9dX4nB6sTq1Zp8Lc"
xsrfKey: "a7f3K9mP2xQ8vL1z9dX4nB6sTq1Zp8Lc"
createNetworkPolicy: false
database:
password: "VMware123!VMware123!"
type: internal
enableContourHttpProxy: true
enableNginxLoadBalancer: false
harborAdminPassword: "VMware123!VMware123!"
hostname: harbor-vks.workernode.lab
ingress:
className: contour
jobservice:
replicas: 1
secret: "H3x9pV6nT2bQ8mZa9dX4nB6sTq1Zp8Lc"
logLevel: info
metrics:
core:
path: /metrics
port: 8001
enabled: false
exporter:
path: /metrics
port: 8001
jobservice:
path: /metrics
port: 8001
registry:
path: /metrics
port: 8001
namespace: tanzu-system-registry
network:
ipFamilies: []
persistence:
imageChartStorage:
azure:
accountkey: base64encodedaccountkey
accountname: accountname
container: containername
realm: core.windows.net
disableredirect: false
filesystem:
rootdirectory: /storage
gcs:
bucket: bucketname
chunksize: 5242880
encodedkey: base64-encoded-json-key-file
oss:
accesskeyid: accesskeyid
accesskeysecret: accesskeysecret
bucket: bucketname
region: regionname
s3:
bucket: bucketname
encrypt: false
region: us-west-1
secure: true
skipverify: false
storageclass: STANDARD
v4auth: true
swift:
authurl: https://storage.myprovider.com/v3/auth
container: containername
password: password
username: username
type: filesystem
persistentVolumeClaim:
database:
accessMode: ReadWriteOnce
existingClaim: ""
size: 1Gi
storageClass: "k8s-nfs-policy"
subPath: ""
jobservice:
jobLog:
accessMode: ReadWriteOnce
existingClaim: ""
size: 1Gi
storageClass: "k8s-nfs-policy"
subPath: ""
redis:
accessMode: ReadWriteOnce
existingClaim: ""
size: 1Gi
storageClass: "k8s-nfs-policy"
subPath: ""
registry:
accessMode: ReadWriteOnce
existingClaim: ""
size: 10Gi
storageClass: "k8s-nfs-policy"
subPath: ""
trivy:
accessMode: ReadWriteOnce
existingClaim: ""
size: 5Gi
storageClass: "k8s-nfs-policy"
subPath: ""
port:
https: 443
proxy:
httpProxy: ""
httpsProxy: ""
noProxy: 127.0.0.1,localhost,.local,.internal
redis:
external:
addr: 192.168.0.2:6379
coreDatabaseIndex: 0
jobserviceDatabaseIndex: 1
password: ""
registryDatabaseIndex: 2
trivyAdapterIndex: 5
type: internal
registry:
replicas: 1
secret: "kL8v2Qm9sX1cR7tP9dX4nB6sTq1Zp8Lc"
resources:
containers:
- cpuLimit: 1000m
cpuRequest: 500m
memoryLimit: 2Gi
memoryRequest: 512Mi
name: core
- cpuLimit: 2000m
cpuRequest: 1000m
memoryLimit: 2Gi
memoryRequest: 1Gi
name: database
- cpuLimit: 1000m
cpuRequest: 500m
memoryLimit: 2Gi
memoryRequest: 512Mi
name: jobservice
- cpuLimit: 300m
cpuRequest: 100m
memoryLimit: 256Mi
memoryRequest: 128Mi
name: portal
- cpuLimit: 500m
cpuRequest: 200m
memoryLimit: 1Gi
memoryRequest: 256Mi
name: redis
- cpuLimit: 1000m
cpuRequest: 500m
memoryLimit: 2Gi
memoryRequest: 512Mi
name: registry
- cpuLimit: 500m
cpuRequest: 200m
memoryLimit: 512Mi
memoryRequest: 256Mi
name: registryctl
- cpuLimit: 2000m
cpuRequest: 500m
memoryLimit: 4Gi
memoryRequest: 1Gi
name: trivy
- cpuLimit: 300m
cpuRequest: 100m
memoryLimit: 256Mi
memoryRequest: 128Mi
name: exporter
namespaceLimitRange:
defaultCPULimit: 1000m
defaultCPURequest: 300m
defaultMemoryLimit: 2Gi
defaultMemoryRequest: 256Mi
secretKey: "a7f3K9mP2xQ8vL1z"
tlsCertificate:
signingSettings:
additionalDnsNames: []
caIssuer:
ca.crt:
ca.key:
ipAddresses: []
trace:
enabled: false
jaeger:
endpoint: http://hostname:14268/api/traces
otel:
compression: false
endpoint: hostname:4318
insecure: true
timeout: 10
url_path: /v1/traces
provider: jaeger
sample_rate: 1
trivy:
dbRepository: ghcr.io/aquasecurity/trivy-db
enabled: false
gitHubToken: ""
insecure: false
javaDBRepository: ghcr.io/aquasecurity/trivy-java-db
offlineScan: false
replicas: 1
skipJavaDBUpdate: false
skipUpdate: true
timeout: ""
tmpdir: ""
vmciRelayProxy:
enabled: false
- Validate Package Installation
root@image-builder:/home/pj# vcf package installed get harbor --namespace package-installed NAMESPACE: package-installed NAME: harbor PACKAGE-NAME: harbor.kubernetes.vmware.com PACKAGE-VERSION: 2.14.2+vmware.1-vks.1 STATUS: Reconcile succeeded CONDITIONS: - status: "True" type: ReconcileSucceededroot@image-builder:/home/pj# kubectl get all -n tanzu-system-registryNAME READY STATUS RESTARTS AGEpod/harbor-core-88c6f97b7-nnrtj 1/1 Running 0 3m10spod/harbor-database-0 1/1 Running 0 3m9spod/harbor-jobservice-79b49bffb9-qq7lx 1/1 Running 3 (2m43s ago) 3m9spod/harbor-portal-6776455d9d-xqls9 1/1 Running 0 3m9spod/harbor-redis-0 1/1 Running 0 3m9spod/harbor-registry-5cdc85c444-fn9fl 2/2 Running 0 3m8sNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEservice/harbor-core ClusterIP 10.104.47.121 <none> 443/TCP 3m9sservice/harbor-database ClusterIP 10.108.247.6 <none> 5432/TCP 3m9sservice/harbor-jobservice ClusterIP 10.110.194.175 <none> 443/TCP 3m9sservice/harbor-portal ClusterIP 10.102.80.48 <none> 443/TCP 3m9sservice/harbor-redis ClusterIP 10.96.214.168 <none> 6379/TCP 3m9sservice/harbor-registry ClusterIP 10.107.117.57 <none> 5443/TCP,8443/TCP 3m10sNAME READY UP-TO-DATE AVAILABLE AGEdeployment.apps/harbor-core 1/1 1 1 3m10sdeployment.apps/harbor-jobservice 1/1 1 1 3m9sdeployment.apps/harbor-portal 1/1 1 1 3m9sdeployment.apps/harbor-registry 1/1 1 1 3m8sNAME DESIRED CURRENT READY AGEreplicaset.apps/harbor-core-88c6f97b7 1 1 1 3m10sreplicaset.apps/harbor-jobservice-79b49bffb9 1 1 1 3m9sreplicaset.apps/harbor-portal-6776455d9d 1 1 1 3m9sreplicaset.apps/harbor-registry-5cdc85c444 1 1 1 3m8sNAME READY AGEstatefulset.apps/harbor-database 1/1 3m9sstatefulset.apps/harbor-redis 1/1 3m9s
- Retrieve the external endpoint IP of Harbor and create the corresponding PTR and A records in the DNS server using the hostname specified in the harbor-data-values.yaml file.
root@image-builder:/home/pj# kubectl get service envoy -n tanzu-system-ingress
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
envoy LoadBalancer 10.101.112.187 172.16.50.11 80:30972/TCP,443:30301/TCP 40m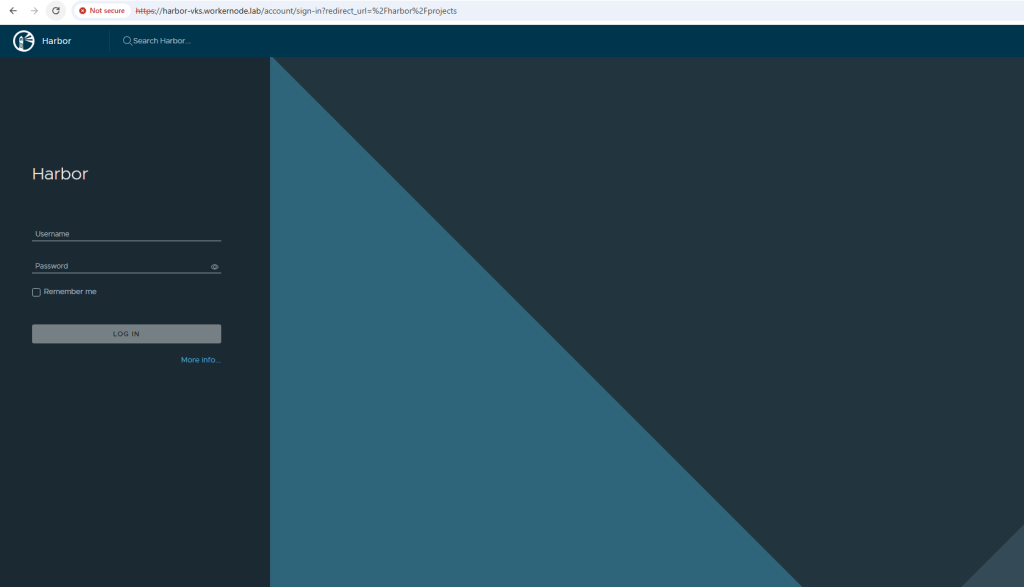
Conclusion
Deploying Harbor on VKS clusters in an air-gapped environment is a critical step toward building a secure, self-sufficient Kubernetes platform. While the absence of external connectivity introduces additional preparation and operational complexity, it also strengthens control over the software supply chain and ensures compliance with strict enterprise security requirements.
By carefully pre-staging container images, mirroring required packages, and configuring Harbor using the VKS Standard Package, organizations can establish a reliable internal registry that fully supports application deployment in disconnected environments. Once operational, Harbor becomes the central backbone for managing container images, enabling secure storage, vulnerability scanning, and controlled distribution across the cluster.
With the right planning and configuration, Harbor empowers teams to maintain agility and automation in Kubernetes workflows—even in fully isolated environments.
Disclaimer: All posts, contents and examples are for educational purposes in lab environments only and does not constitute professional advice. No warranty is implied or given. The user accepts that all information, contents, and opinions are my own. They do not reflect the opinions of my employer.

Leave a comment